Uncategorized
CSS Makes Your Images Look Good. A VPS Makes Them Load Fast.
You want a beautiful, responsive site where every image is perfectly framed, regardless of the user’s screen size. In our previous guide to CSS object-fit, we mastered the art of making images visually fit into any container without distortion.
If you followed that guide, your site probably looks fantastic.
But there is a hidden trap with modern CSS image techniques. If you aren’t careful, you might be creating a beautiful, slow-loading disaster that tanks your SEO and frustrates mobile users.
Here is why CSS is only half the battle, and why serious websites need the infrastructure to back up their design.
The “Invisible” Problem with CSS Resizing
CSS properties like object-fit and width: 100% handle the display dimensions of an image. They do absolutely nothing to the file size.
Imagine you upload a stunning, high-resolution photograph straight from Unsplash. It’s 4000 pixels wide and weighs in at 5MB. You place it in a small “Recent Posts” card on your homepage that is only 300 pixels wide.
You use CSS:
.thumbnail {
width: 300px;
height: 200px;
object-fit: cover;
}
Visually, it looks perfect. The browser shrinks it down neatly.
But here is the reality: Every visitor to your homepage—even someone on a shaky 4G mobile connection—has to download that entire 5MB file, just to view a tiny 300px thumbnail.
This kills your Core Web Vitals scores, increases bounce rates, and wastes your users’ data.
The Solution: Dynamic, Server-Side Optimization
To have a site that looks great and loads instantly, you need to serve images that are expertly sized for the exact slot they are filling.
You shouldn’t serve that 4000px image. You should serve a 300px version that has been compressed and converted to a modern format like WebP or AVIF.
You could manually Photoshop every image into five different sizes before uploading, but that’s unmanageable. The professional solution is On-the-Fly Image Optimization.
This means when a user requests an image, your server instantly grabs the original, resizes it perfectly for that specific request, optimizes it, caches it, and delivers the tiny new file.
Why Shared Hosting Can’t Handle the Load
Real-time image manipulation—using heavy-duty libraries like ImageMagick, GD, or Node.js ‘Sharp’—is incredibly CPU-intensive.
If you try to run a dynamic image server on standard cheap shared hosting, one of two things will happen:
-
Your host will throttle your CPU usage, making your images load agonizingly slowly.
-
Your host will flag your account for abusing server resources and shut you down.
Shared hosting is built for serving static text files, not for intense computational tasks like crunching thousands of pixels instantly.
The VPS Advantage
This is the inflection point where a serious project needs to graduate to a Virtual Private Server (VPS).
A VPS gives you dedicated slices of CPU and RAM that are yours alone. You aren’t fighting for resources with hundreds of other websites on the same machine.
With a modest VPS, you gain the power to:
-
Run powerful optimization engines: Install Node.js, Python, or advanced PHP modules to handle image resizing in milliseconds.
-
Automate Next-Gen Formats: Automatically convert JPEGs to highly efficient WebP or AVIF formats on the fly.
-
Improve Core Web Vitals: Serve the exact file size needed, drastically lowering your Largest Contentful Paint (LCP) times.
Take Control of Your Infrastructure
Don’t let heavy files undermine your beautiful CSS work. By moving to a VPS, you gain the control and power necessary to ensure your images are as lightweight as they are good-looking.
It’s the difference between a site that looks professional and a site that performs professionally.
Meta Pixel vs Conversions API (CAPI)
For years, most advertisers relied on the Meta Pixel to understand what happened after someone clicked an ad. You installed a small snippet of code on your site, and Meta could see page views, leads, and purchases inside the browser. It worked — until the internet changed.
Privacy updates from Apple, browser-level tracking prevention, and widespread ad blockers have significantly reduced how much data browser-based tracking can reliably collect. As a result, many advertisers now see gaps in reporting, delayed attribution, or missing conversions — even when campaigns are clearly driving results.
This is where Meta’s Conversions API (CAPI) comes in.
Instead of relying solely on the user’s browser, CAPI allows conversion events to be sent directly from your server to Meta. This server-side approach makes tracking more resilient to privacy restrictions, improves data accuracy, and gives Meta’s delivery system more consistent signals to optimize campaigns.
That doesn’t mean the Meta Pixel is obsolete — far from it. Pixel and CAPI are designed to work together, each serving a different role in modern ad measurement.
![]()
What is the Meta Pixel?
The Meta Pixel is a browser-based JavaScript tracker that fires events when a user loads a page or takes an action.
How it works
-
Runs in the user’s browser
-
Uses cookies (
_fbp,_fbc) -
Sends events like
PageView,ViewContent,AddToCart,Purchase
Strengths
-
Very easy to install
-
Real-time feedback in Events Manager
-
Captures on-site behavior like scroll depth, clicks, watch time
Limitations (big ones)
-
Blocked by:
-
Ad blockers
-
iOS privacy rules (ITP)
-
Browser tracking prevention
-
-
Loses attribution when cookies expire or are stripped
-
Increasingly under-reports conversions
Best use
Front-end signal discovery (what users do on the page)
What is Conversions API (CAPI)?
CAPI is server-side tracking. Instead of relying on the browser, your server sends events directly to Meta.
If you run a CRM, Shopify, or any big branded platforms chances are CAPI is already part of the system, you would just need to make sure it’s enabled and set up properly.
If you run a more basic website like a WordPress site, or something that doesn’t have built in support, then you would need to either build your own backend server (you can literally do this very easily in DigitalOcean), run it locally (not recommended), or pay to use a service which does all of it for you with a guarantee of ad attribution performance and ad savings. If you’re interested in that last bit, and if you spend a hefty sum per month on Meta ads, you might want to consider looking deeper into this.
How it works
-
Events are sent from:
-
Your backend
-
A tag manager server
-
A custom endpoint
-
-
Can include hashed identifiers:
-
Email
-
Phone
-
IP
-
User agent
-
fbp/fbc (when available)
-
Strengths
-
Not blocked by browsers or ad blockers
-
More stable attribution
-
Better match quality for Meta’s AI
-
Required for advanced attribution and scaling
Limitations
-
More complex to implement
-
Needs proper event deduplication
-
Requires backend or server tooling
Best use
Reliable conversion truth for optimization and reporting
Pixel vs CAPI (quick comparison)
| Area | Meta Pixel | CAPI |
|---|---|---|
| Runs in | Browser | Server |
| Blockable | Yes | No |
| iOS impact | High | Minimal |
| Setup | Easy | Technical |
| Attribution accuracy | Medium → Low | High |
| Required for scale | ❌ | ✅ |
The correct setup (this is the key part)
You should NOT choose Pixel or CAPI.
You should run BOTH.
Why?
-
Pixel captures behavioral signals (what users do)
-
CAPI guarantees conversion delivery
-
Meta deduplicates events using
event_id
Correct flow
-
Pixel fires event in browser
-
Server sends the same event via CAPI
-
Meta deduplicates
-
AI gets cleaner, richer data
-
Delivery and optimization improve
This is exactly how Meta expects serious advertisers to operate in 2026.
When Pixel alone is “good enough”
-
Small spend (<$50/day)
-
Lead gen without backend control
-
Early testing / MVP funnels
Even here, you’re flying partially blind.
When CAPI becomes mandatory
-
Scaling spend
-
iOS-heavy audiences
-
Ecommerce
-
Video + engagement optimization
-
Advanced attribution (multi-touch, offline, CRM)
If you’re doing any serious optimization, Pixel-only is no longer sufficient.
How Meta’s AI actually uses this data
Meta’s delivery system doesn’t just look at conversions — it looks at:
-
Event frequency
-
Signal consistency
-
Identity match quality
-
Engagement depth (watch time, dwell, repeats)
CAPI improves confidence, not just counts.
That’s why campaigns often stabilize after CAPI is implemented — even when reported numbers don’t jump dramatically.
Bottom line
-
Meta Pixel = visibility + behavioral signals
-
CAPI = reliability + optimization fuel
-
Together = modern, scalable tracking
Want it just done for you?
Book a demo with Hyros where they handle everything
Running NordVPN in Docker on DigitalOcean (for Region-Lock Testing)
This guide shows how coders can run NordVPN inside a Docker container on a DigitalOcean Droplet and then route test containers through it to verify geo-based restrictions, region-locked APIs, pricing, or content behavior. If you need help installing NordVPN in a Docker container, you might find this guide on Windows helpful + this guide for MacOS helpful.
⚠️ Important: A VPN inside Docker does not VPN the host.
Only traffic generated by containers using the VPN container’s network is routed through NordVPN. This is intentional and exactly what we want for controlled testing.
Why this setup exists (quick context)
This approach is ideal when you need:
-
Real data-center IPs in specific countries
-
A repeatable, disposable geo-testing environment
-
Isolation between “normal app traffic” and “geo-simulated traffic”
You are not trying to “secure the Droplet” — you’re trying to simulate geography.
Architecture (mental model)
Only containers explicitly attached to the VPN container’s network go through the tunnel.
Click Here To Save With DigitalOcean Discount
Requirements
-
DigitalOcean Droplet (Ubuntu 22.04 or newer) – how to create a droplet
-
Docker + Docker Compose installed
-
NordVPN account
-
NordVPN login token (required for non-GUI Docker usage) – watch this video it shows how to get service credentials
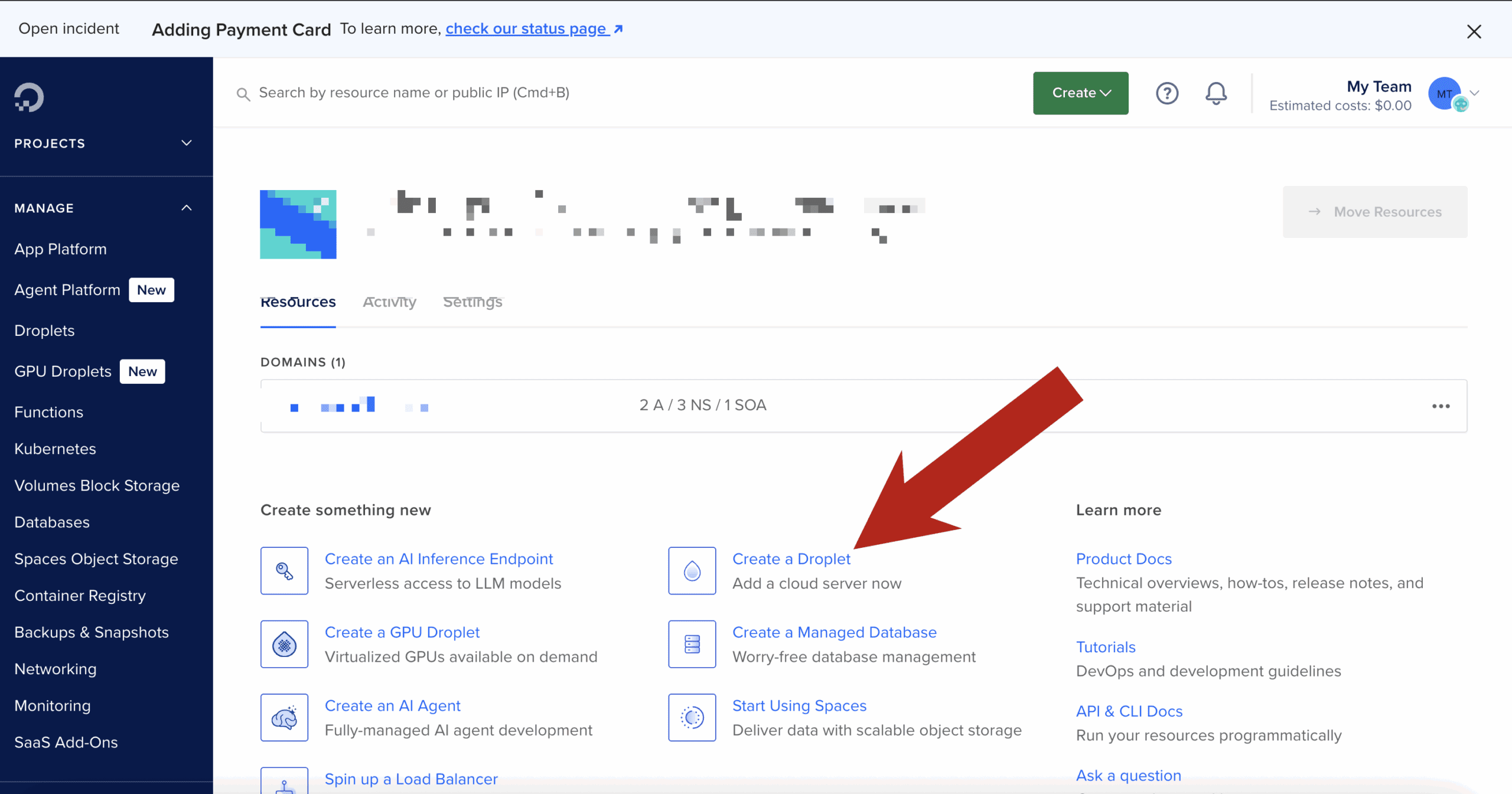
Step 1: Create the Droplet & install Docker
SSH into your Droplet, then install Docker:
Verify:
Step 2: Build the official NordVPN Docker image
This follows NordVPN’s documented approach, with no shortcuts.
Create a project directory
Create the Dockerfile
Paste:
Build the image:
Step 3: Run the NordVPN container (VPN only)
Why these flags matter
-
NET_ADMIN→ required to create VPN routes -
/dev/net/tun→ required for tunnel interfaces -
Hostname lock → prevents identity changes across restarts
Step 4: Authenticate using a NordVPN token
Inside the container:
Then connect to a country:
Confirm:
At this point, this container is fully VPN-connected.
Step 5: Turn the NordVPN container into a “VPN gateway”
Open a new terminal (outside the container).
Any container that uses:
will share the NordVPN container’s network stack — meaning all outbound traffic exits via the VPN.
Step 6: Run a geo-test container through the VPN
Example: test IP + country
Expected output:
If you see your Droplet’s region instead, the container is not attached to the VPN network.
Step 7: Run real code through the VPN
Node.js / Python / Playwright / curl / Postman
Any tool works the same way.
Example with a Node container:
Now:
-
API calls
-
OAuth redirects
-
Pricing endpoints
-
Content checks
…all behave as if they originate from the chosen country.
Switching regions (fast testing loop)
Inside the NordVPN container:
Then re-run your test containers.
This gives you a tight, repeatable geo-testing loop.
Common issues & fixes
/dev/net/tun missing
If missing:
Auth fails
-
Use token-based login
-
Do not use email/password inside Docker
IPv6 leaks or odd routing
If you suspect IPv6 issues, explicitly disable it at the container level:
(Some Nord docs mention this, but the value is commonly mis-documented.)
Click Here To Save With DigitalOcean Discount
Best Keyboard for Coding & Programming
If you write code for a living, your keyboard isn’t an accessory — it’s one of your most important tools.
Most developers will type millions of keystrokes per year, often in long, focused sessions. Yet many still use whatever keyboard came in the box or whatever was cheapest on Amazon. The result? Wrist pain, shoulder tension, fatigue, and in some cases real repetitive strain injuries.
The good news: the right keyboard can dramatically improve comfort, speed, accuracy, and even focus.
This guide breaks down exactly how to choose the best keyboard for coding based on real developer workflows — and the specific models that consistently perform well for programmers.
Whether you’re a web developer, software engineer, data engineer, or student learning to code, this will help you make a smart, future-proof choice.
Click for my favorite keyboard
Who This Guide Is For
This article is written for:
-
Software engineers & web developers
-
Indie hackers & SaaS builders
-
Data engineers & analysts
-
Students learning to code
-
Anyone spending multiple hours per day typing in an IDE or terminal
If you code regularly, this applies to you.
Why Your Keyboard Matters More for Coding Than You Think
Coding is not casual typing.
You’re constantly using:
-
Symbols (
{ } [ ] ( ) ; : < >) -
Modifier keys (Cmd, Ctrl, Alt, Shift)
-
Navigation (arrows, home/end, page up/down)
-
Shortcuts and key combos
Over time, small ergonomic issues compound. A bad layout, poor key feel, or awkward wrist angle can lead to:
-
Wrist and forearm pain
-
Shoulder and neck tension
-
Slower typing and more errors
-
Fatigue that affects focus and productivity
Most developers don’t notice until something starts hurting. By then, it’s already a problem.
A good keyboard won’t magically fix everything — but the right layout, switches, and ergonomics can make a massive difference over months and years.
How to Choose the Right Keyboard for Coding
Instead of jumping straight to product recommendations, let’s break down the 5 factors that actually matter for programmers.
This is the framework you should use before buying anything.
1. Layout: Full, TKL, 75%, 60%, or Split?
Layout determines how much movement your hands and shoulders make all day. This matters more than most people realize.
Full-Size (100%)
Includes number pad. Good for:
-
Data-heavy work
-
Finance, spreadsheets, analytics
-
Some backend workflows
Downside: wider reach, more shoulder movement.
TKL (Tenkeyless) – 87 keys
No number pad. Very popular with developers.
Good balance of:
-
Compact size
-
Full navigation cluster
-
Minimal learning curve
75% Layout
Slightly more compact than TKL but keeps arrows + nav keys.
One of the best layouts for most programmers.
60% Layout
Very compact. No dedicated arrows or nav keys.
RK Royal Kludge RK61
Good for:
-
Minimalist setups
-
Vim users
-
Travel
Downside: heavy reliance on layers. Not ideal for everyone.
Split / Ergonomic Layouts
Two halves, often tented.
Good for:
-
Wrist pain
-
Shoulder issues
-
Long daily sessions
Downside: learning curve.
Rule of thumb:
If you use arrow keys, home/end, and page navigation a lot (most devs do), don’t go smaller than 75%.
2. Switch Type: Linear vs Tactile vs Clicky (In Coder Terms)
This is about feel and feedback, not gaming performance.
Tactile (e.g. Brown-style)
-
Small bump when key actuates
-
Great feedback for accuracy
-
Popular among developers
Linear (e.g. Red-style)
-
Smooth, no bump
-
Fast and quiet
-
Good for speed and low fatigue
Clicky (e.g. Blue-style)
-
Loud, clicky feedback
-
Generally not recommended for shared spaces
-
Can be fatiguing over long sessions
Most programmers prefer tactile or linear switches.
Clicky switches are fun, but not ideal for 8-hour workdays.
3. Key Feel & Fatigue: Low Profile vs Standard
Low-profile keyboards (like laptop-style keys) have:
-
Shorter travel
-
Less finger movement
-
Lower learning curve
Standard mechanical boards have:
-
Deeper travel
-
More tactile feedback
-
Often better long-term comfort for heavy typists
There is no universal “best” here — it depends on:
-
Your typing style
-
Hand size
-
Desk height
-
Whether you came from laptops or desktops
4. Programmability & Layers (Underrated for Coders)
This is huge and often ignored.
Keyboards that support QMK, VIA, or custom remapping let you:
-
Move symbols to easier positions
-
Create layers for navigation
-
Add macros for repetitive actions
-
Optimize layouts for your IDE
If you use:
-
Vim / Neovim
-
Heavy keyboard shortcuts
-
Custom workflows
Then programmability is a major advantage.
5. Ergonomics & Wrist Health
If you code 4–10 hours a day, this matters.
Key ergonomic factors:
-
Wrist angle
-
Shoulder width
-
Forearm rotation
-
Key reach
Split keyboards and tented designs reduce:
-
Ulnar deviation (bending wrists sideways)
-
Shoulder tension
-
Forearm strain
If you’ve ever had:
-
Wrist pain
-
Numbness
-
Tingling
-
Elbow issues
You should strongly consider an ergonomic layout.
Best Keyboards for Coding by Category
Now that you know what matters, here are proven, well-regarded options for different developer profiles.
These are grouped by use case, not just price.
Best All-Around Keyboard for Coding
Keychron K Pro Series (K8 Pro, K2 Pro, K3 Pro)
Who it’s for:
Developers who want one solid keyboard that works across Mac, Windows, and Linux without fuss.
Why it’s great for coding:
-
Excellent 75% / TKL layouts
-
Hot-swappable switches
-
QMK/VIA support for remapping
-
Clean, professional look (no gamer nonsense)
Pros:
-
Great typing feel out of the box
-
Wireless + wired options
-
Strong community support
Cons:
-
Slightly tall (may need a wrist rest)
-
Not split/ergonomic
Bottom line:
If you want a safe, high-quality choice that “just works” for programming, this is it.
Best Keyboard for Long Coding Sessions
Logitech MX Keys S
Who it’s for:
Developers who value comfort, low fatigue, and a laptop-like feel.
Why it’s great for coding:
-
Low-profile keys reduce finger travel
-
Excellent stability and spacing
-
Great for multi-device workflows
-
Quiet (ideal for calls and shared spaces)
Pros:
-
Extremely comfortable for long sessions
-
Wireless, multi-device pairing
-
Clean professional design
Cons:
-
Not mechanical
-
Limited programmability
Bottom line:
If you code all day and want maximum comfort with minimal learning curve, this is hard to beat.
Best Compact Keyboard for Developers
Keychron K6 / K3 (65% / 75%)
Who it’s for:
Developers with limited desk space or who travel.
Why it’s great for coding:
-
Keeps arrow keys (unlike many 60% boards)
-
Compact footprint
-
Solid build quality
Pros:
-
Portable
-
Good layout for IDE work
-
Affordable
Cons:
-
Smaller keys = adjustment period
-
Less ergonomic than larger boards
Bottom line:
A great option if you want compact without sacrificing usability.
Best Ergonomic Keyboard for Programmers
Kinesis Advantage2 / Advantage360
or
Moonlander / Ergodox EZ
Who it’s for:
Developers with wrist, elbow, or shoulder pain — or those who want to prevent it.
Why it’s great for coding:
-
Split layout reduces wrist angle
-
Tented design improves posture
-
Fully programmable
-
Designed for heavy typists
Pros:
-
Excellent ergonomics
-
Highly customizable
-
Long-term comfort
Cons:
-
Steep learning curve
-
Expensive
-
Looks weird (you’ll get comments)
Bottom line:
If you code for a living and plan to do it for years, this is an investment in your health.
Best Budget Keyboard for Coding
Royal Kludge (RK) Series – RK68, RK84, RK61
Who it’s for:
Students, early-career devs, or anyone on a budget.
Why it’s great for coding:
-
Mechanical feel at low price
-
Decent layouts
-
Hot-swap on many models
Pros:
-
Affordable
-
Surprisingly solid
-
Good starter boards
Cons:
-
Software is mediocre
-
Build quality not premium
Bottom line:
If you want mechanical without spending a lot, these punch above their weight.
What Developers and Reddit Consistently Say Matters
Across developer and keyboard communities, the same themes come up over and over:
-
Comfort beats aesthetics
-
Layout matters more than brand
-
Tactile or linear switches are preferred for work
-
Programmability is underrated
-
Ergonomics becomes important sooner than you think
Many developers report that once they switched to a better keyboard, they:
-
Made fewer typing errors
-
Felt less fatigue
-
Had less wrist or shoulder pain
-
Enjoyed coding more
That’s not marketing hype — it’s a real productivity and health factor.
Common Mistakes Developers Make When Buying a Keyboard
Avoid these:
1. Going Too Small Too Fast
Jumping straight to 60% can be frustrating if you rely on arrows and nav keys.
2. Buying Gaming Keyboards for Work
RGB and “speed” features don’t equal comfort or productivity.
3. Ignoring Ergonomics
Pain creeps up slowly. By the time it’s bad, it’s harder to fix.
4. Not Considering Desk Setup
Keyboard choice should match:
-
Desk height
-
Chair height
-
Monitor position
-
Arm angle
Quick Decision Guide
If you want a fast answer:
-
I code 6–10 hours/day and want comfort → Logitech MX Keys, ergonomic split keyboard
-
I want one great mechanical board → Keychron K Pro series
-
I use Vim and love minimalism → 60–65% board with layers
-
I have wrist/shoulder pain → Split ergonomic keyboard
-
I’m on a budget → Royal Kludge series
FAQ
Are mechanical keyboards better for coding?
Not automatically. Many developers love them for feedback and feel, but low-profile boards like MX Keys are also excellent for long sessions.
Is a 60% keyboard good for programming?
It can be, especially for Vim users, but many developers find 75% or TKL layouts more practical.
What do most software engineers use?
There’s no single standard, but 75% / TKL mechanical keyboards and low-profile wireless boards are extremely common.
Are split keyboards worth it?
If you have pain or type for long hours daily, yes — many devs swear by them.
Final Thoughts
If you’re spending thousands of hours a year writing code, your keyboard is not the place to cheap out.
The right keyboard won’t just feel better — it can:
-
Reduce fatigue
-
Improve accuracy
-
Prevent long-term injury
-
Make coding more enjoyable
Take a little time to choose one that fits your workflow, your body, and your future.
Your hands will thank you.
Click for my favorite keyboard
Best VPNs for Coders & Developers
Advanced Features, Docker Support, CLI Automation, Mesh Networking & Real Dev Workflows
Most VPN reviews are written for people trying to watch Netflix in another country.
This guide is for people who run Docker, SSH into servers, build automation, scrape data, and actually care if their network stack breaks.
If you’re a developer, infra builder, automation engineer, or someone running a home lab, this is the VPN guide you’ve been looking for.
Click for my favorite vpn provider
Why Developers Actually Use VPNs (Not the Marketing Reasons)
Developers don’t use VPNs to “stay anonymous.” They use them because real-world dev workflows create real-world problems.
1. Secure Access to Servers & Infrastructure
If you’re SSH’ing into production, internal dashboards, or client systems from coffee shops, airports, or coworking spaces, a VPN adds a secure tunnel before you even hit your SSH keys and MFA.
It’s not about paranoia. It’s about reducing your attack surface.
2. Working on Hostile or Restricted Networks
Hotels, corporate Wi-Fi, conference networks, and international travel networks often:
-
block ports
-
inspect traffic
-
throttle connections
-
or straight up break SSH / Git
A VPN with obfuscation or WireGuard support often fixes this instantly.
3. Geo-Testing & Region Simulation
Developers frequently need to test:
-
regional pricing
-
localized content
-
country-specific APIs
-
ad delivery behavior
A VPN lets you see what users in Germany, Canada, or Singapore actually see — without spinning up servers in every region.
4. Scraping, Automation & Data Collection
If you’re running:
-
Playwright
-
Puppeteer
-
cron-based scrapers
-
API polling jobs
…you already know IP reputation matters. Routing automation traffic through a VPN (especially in Docker) is a clean way to:
-
avoid blocks
-
separate identities
-
and reduce risk
5. Home Lab & Internal Network Access
If you run:
-
a NAS (Synology, QNAP, etc.)
-
internal APIs
-
dev boxes
-
self-hosted services
A VPN or mesh network lets you access all of that remotely without opening ports to the internet.
This is a massive quality-of-life improvement.
What Makes a VPN “Developer-Grade”
Most “best VPN” lists talk about streaming and device counts. Developers care about completely different things.
1. Performance & Latency
Not just raw speed — but:
-
low ping
-
stable connections
-
long-lived sessions
This matters for:
-
SSH
-
streaming logs
-
WebSockets
-
remote debugging
WireGuard support is a big deal here.
2. Linux & Headless Support
If a VPN doesn’t:
-
support Linux cleanly
-
offer a CLI
-
work in headless environments
…it’s not a serious option for developers.
3. Split Tunneling (The Actually Useful Kind)
Developers use split tunneling to:
-
route Docker traffic through VPN
-
keep localhost, databases, and internal APIs off VPN
-
avoid breaking webhooks and tunnels
This is essential when you mix local dev + remote services.
4. Stability Over Flash
Random disconnects kill:
-
SSH sessions
-
CI jobs
-
long-running scripts
A “slower but stable” VPN is often better than a fast, flaky one.
5. Configurability & Control
Developers want:
-
protocol choice (WireGuard, OpenVPN)
-
port control
-
predictable routing
-
real kill switch behavior
Not “one button and pray.”
Advanced & Lesser-Known VPN Features Developers Actually Use
This is where most articles stop — and where real value starts.
1. Running VPNs Inside Docker Containers
This is huge for infra builders and automation devs.
Instead of running a VPN on your host machine, you can:
-
run the VPN client in its own container
-
route other containers through it
-
isolate traffic cleanly
-
avoid touching your host network stack
NordVPN in Docker
Nord officially supports this.
Common pattern:
-
one container runs NordVPN
-
other containers use
network_mode: service:nordvpn
Use cases:
-
Playwright scrapers
-
Puppeteer jobs
-
n8n workflows
-
API polling services
This is extremely clean for automation stacks.
ProtonVPN in Docker
Not as officially marketed, but widely used via:
-
WireGuard configs
-
OpenVPN configs
-
community images
Often used in:
-
CI runners
-
scraping pipelines
-
test harnesses
Private Internet Access (PIA) in Docker
Very popular with power users because:
-
highly configurable
-
supports port forwarding
-
easy to script
If you care about inbound connections or fine-grained control, PIA is strong here.
2. CLI Support for Automation & Headless Environments
This is non-negotiable for serious dev workflows.
With a CLI you can:
-
spin up a server
-
connect VPN
-
run a job
-
disconnect VPN
-
tear down server
All in a script.
VPNs with real CLI support:
-
NordVPN (Linux CLI)
-
ProtonVPN CLI
-
PIA CLI
-
Mullvad CLI
This is essential for:
-
cron jobs
-
CI pipelines
-
ephemeral servers
3. Mesh Networking (Nord Meshnet, Tailscale, ZeroTier)
This is one of the most underutilized features in the dev world.
Nord Meshnet
Nord quietly added Meshnet, which is essentially:
a private, device-to-device network built into NordVPN
What it lets you do:
-
access your home NAS remotely
-
connect dev machines together
-
hit internal APIs from anywhere
-
avoid port forwarding entirely
For home lab users, this is huge.
Tailscale
Tailscale is increasingly preferred by developers because:
-
it’s built on WireGuard
-
no exit nodes
-
no performance penalty
-
perfect for internal networks
If you want:
-
dev → NAS
-
dev → server
-
dev → internal tools
Tailscale is often better than a traditional VPN.
4. Port Forwarding
Most consumer VPNs hide or remove this. Developers actively need it.
Use cases:
-
webhook testing
-
inbound API callbacks
-
peer-to-peer services
VPNs that support it:
-
PIA
-
AirVPN
If you need inbound connectivity, this matters.
5. Dedicated IPs
Some APIs and enterprise systems:
-
block shared VPN IPs
-
require allowlisting
Dedicated IPs solve this.
Offered by:
-
NordVPN
-
PIA
-
CyberGhost
This is important for:
-
client systems
-
production dashboards
-
IP-restricted services
6. Obfuscation for Restricted Networks
If you work from:
-
corporate networks
-
hotels
-
international locations
Obfuscated servers help:
-
hide VPN usage
-
bypass restrictions
-
keep SSH and Git working
Supported by:
-
NordVPN
-
ProtonVPN
-
Surfshark
Feature Matrix – VPNs Compared for Developers
Here’s the at-a-glance view of what actually matters:
| Feature / VPN | NordVPN | ProtonVPN | PIA | Surfshark | ExpressVPN | Tailscale |
|---|---|---|---|---|---|---|
| Docker support | ✅ Official | ⚠️ Community | ✅ Popular | ⚠️ Limited | ❌ | ❌ |
| CLI support | ✅ | ✅ | ✅ | ❌ | ❌ | n/a |
| Mesh networking | ✅ Meshnet | ❌ | ❌ | ❌ | ❌ | ✅ |
| Port forwarding | ❌ | ❌ | ✅ | ❌ | ❌ | ❌ |
| Split tunneling | ✅ | ✅ | ✅ | ✅ | ❌ | n/a |
| WireGuard | ✅ | ✅ | ✅ | ✅ | ❌ | n/a |
| Dedicated IP | ✅ | ❌ | ✅ | ❌ | ❌ | ❌ |
| Linux support | ✅ | ✅ | ✅ | ⚠️ | ⚠️ | ✅ |
Click for my favorite vpn provider
Best VPNs for Coders – Deep Dives
NordVPN – Best All-Around for Infra & Automation Devs
Best for: Docker, mesh networking, general infra work
Why developers use it:
-
official Docker support
-
CLI on Linux
-
WireGuard (NordLynx)
-
Meshnet for internal access
Hidden strength:
-
Meshnet + Docker is a very powerful combo for home labs and automation stacks.
Limitation:
-
no port forwarding
ProtonVPN – Best for Privacy-Focused Developers
Best for: privacy, audits, open-source workflows
Why devs like it:
-
audited no-logs policy
-
open-source clients
-
excellent split tunneling
-
strong Linux support
Hidden strength:
-
great balance of privacy + usability
Limitation:
-
no port forwarding
-
Docker usage is less official
Private Internet Access (PIA) – Best for Power Users
Best for: configurability, inbound connections, scripting
Why devs use it:
-
port forwarding
-
CLI support
-
extremely configurable
-
works well in Docker
Hidden strength:
-
one of the few mainstream VPNs that still respects power users
Limitation:
-
UI is not pretty
-
less “polished” than Nord
Surfshark – Best Budget Option for Multi-Device Devs
Best for: freelancers with lots of devices
Why devs use it:
-
unlimited devices
-
decent WireGuard performance
Limitation:
-
weaker CLI and advanced features
-
not ideal for infra-heavy workflows
ExpressVPN – Best for Simplicity & Stability
Best for: people who want it to just work
Why devs use it:
-
extremely stable
-
good global coverage
Limitation:
-
weak Linux support
-
no Docker or CLI focus
-
not dev-oriented
Mesh VPNs & Self-Hosted Alternatives
Tailscale – Best for Internal Dev Networks
If you run:
-
NAS
-
dev servers
-
internal APIs
Tailscale is often better than a traditional VPN.
It gives you:
-
private IPs
-
zero config
-
no port forwarding
-
direct device-to-device access
This is perfect for home labs.
ZeroTier
Similar to Tailscale but more manual. Good for:
-
small teams
-
labs
-
experimental setups
WireGuard (Self-Hosted)
If you want:
-
full control
-
no third-party trust
-
your own VPN server
WireGuard on a VPS is excellent.
This is for people who are comfortable with:
-
networking
-
firewall rules
-
server management
Outline VPN
Simple self-hosted option. Good for:
-
small teams
-
internal access
-
minimal configuration
VPNs in Real Dev Workflows
VPN + Docker + Local Dev
Common patterns:
-
VPN container + service containers
-
split tunneling to avoid breaking localhost
-
routing scrapers through VPN only
This is extremely clean for automation.
VPN + SSH + Production Servers
Best practice:
-
VPN → bastion → prod
-
restrict prod to VPN IPs
-
no public SSH
Much safer.
VPN + CI/CD
Usually:
-
not needed for cloud pipelines
-
useful for:
-
on-prem runners
-
restricted APIs
-
internal systems
-
VPN + Scraping & Automation
Use VPNs to:
-
avoid IP bans
-
separate identities
-
protect your real IP
Combine with:
-
rate limiting
-
respectful crawling
-
legal compliance
VPN + Home Lab / NAS
This is one of the best uses.
Instead of:
-
opening ports
-
exposing services
You get:
-
private access
-
zero exposure
-
much better security
Mesh VPNs shine here.
Click for my favorite vpn provider
Common Problems & Fixes
“VPN broke my Docker networking”
Use:
-
split tunneling
-
network_mode: service:vpn -
or route only specific containers
“I can’t access localhost on VPN”
Exclude localhost from VPN or use split tunneling.
“npm install is slow on VPN”
Change DNS, switch protocol to WireGuard, or exclude npm traffic.
“SSH drops when VPN reconnects”
Use:
-
autossh
-
keepalive settings
-
more stable protocol
“Webhooks fail on VPN”
Likely blocked inbound traffic. Use:
-
port forwarding (PIA)
-
tunnel services
-
or exclude that service from VPN
VPN vs Corporate VPN vs Mesh VPN
| Use Case | Best Option |
|---|---|
| Freelance dev | Nord / Proton |
| Agency dev | Nord + Meshnet |
| Infra builder | Tailscale / WireGuard |
| Home lab | Tailscale / Nord Meshnet |
| Scraper dev | PIA / Nord Docker |
Key idea:
-
Traditional VPN = outbound privacy + security
-
Corporate VPN = company access
-
Mesh VPN = internal network access
They solve different problems.
Final Recommendations – Pick Based on Your Stack
If you’re:
-
Infra-heavy / automation dev:
→ NordVPN + Docker -
Privacy-focused dev:
→ ProtonVPN -
Power user with inbound needs:
→ PIA -
Home lab / NAS user:
→ Tailscale or Nord Meshnet -
Solo freelancer:
→ Surfshark
Click for my favorite vpn provider
Top VPS Hosting Providers in 2026 (And How to Choose the Right One)
If you’re ready to level up your hosting, Virtual Private Servers (VPS) offer a perfect middle ground between affordable shared hosting and expensive dedicated servers. Whether you’re building an app, running an online store, or launching a digital agency, a VPS gives you more speed, flexibility, and control.
But with so many VPS providers, how do you choose the right one?
This post breaks down what to look for, how VPS compares to other hosting options, and which providers offer the best value in 2026.
What Is VPS Hosting (and Why It Matters)
VPS hosting gives you your own slice of a physical server. Unlike shared hosting, where multiple users compete for the same resources, VPS environments are isolated — giving you better performance and security. You’ll get root access, more RAM, and the freedom to install custom software or run complex websites.
Key advantages:
- Greater speed and uptime
- Ability to scale as your site grows
- Full control over server settings
You can also choose between managed VPS (where the hosting company handles updates and maintenance) or unmanaged VPS (you’re on your own — but with more flexibility and lower cost).
What to Look For in a VPS Host
Not all VPS providers are created equal. Here are the features that matter most:
- SSD or NVMe storage: Faster load times and performance
- Scalability: Upgrade resources easily without downtime
- Support: 24/7 live chat or ticket support is a must
- Data centers: Choose a provider close to your target audience
- Control panels: Do you prefer cPanel, Plesk, or SPanel?
- Pricing: Look for fair monthly rates — and beware of high renewal costs
- Backups: Automatic snapshots are a bonus
- Security: Firewalls, DDoS protection, and SSLs should be standard
Click Here For My Favorite VPS Provider
The Best VPS Hosting Providers in 2026
Here’s a closer look at the top VPS options this year, based on price, performance, and who they’re best suited for.
🚀 DigitalOcean — Best for Developers
- From ~$4/month – low entry cost with predictable pricing
- Instant server deployment – launch a VPS in under a minute
- Hourly billing – pay only for what you use
- Easy vertical scaling – upgrade resources as you grow
- Developer-friendly dashboard – simple, clean, no bloat
- Strong API & CLI – built for automation and workflows
- Multiple server types – match compute to your workload
- Global data centers – low latency worldwide
- SSD-backed performance – fast disk and networking
- Built-in ecosystem – databases, storage, Kubernetes, load balancers
- Minimal learning curve – no AWS-style complexity
- Ideal for apps & startups – fast to build, easy to scale
- Click For My Favorite VPS Provider
🔧 Linode (Akamai) — Best for Transparency
- From $5/month
- Predictable pricing, excellent documentation, wide distro support
- Great for technical users
🧪 Vultr — Best OS Flexibility & Automation
- From $5/month
- Latest Linux distros, powerful API, solid security
- Perfect for budget-conscious devs needing variety
🌐 Kamatera — Best Custom Configurations
- From ~$4/month
- Global data centers, custom specs, 30-day free trial
- Ideal for international teams and Windows VPS
💰 Hostinger — Best Budget VPS
- From $5.99/month (4GB RAM)
- AI help, NVMe SSD, robust DDoS protection
- Great for small businesses or beginners
⚡ Hosting (previously A2) — Best for Speed
- From $7.99/month (unmanaged), $39.99 (managed)
- Turbo servers, anytime refund, free cPanel
- Great if speed is a priority
📦 InMotion Hosting — Best for Small Businesses
- From $14.99/month (managed)
- NVMe storage, 24/7 U.S. support, generous resources
- Ideal for growing companies
💡 Namecheap — Best Value VPS for Existing Users
- From $6.88/month
- Reliable SSD performance, easy-to-manage server
- Perfect for budget-conscious site owners
🛡️ OVHcloud — Best for EU Users & Security
- From ~$5/month
- DDoS protection, custom ISO, great EU coverage
- Strong choice for technical European users
🔐 ScalaHosting — Best for Business-Grade Security
- From $29.95/month (managed VPS)
- Daily backups, SPanel, premium support
- Great for mission-critical sites
Click Here For Our Favorite VPS Provider
Summary Table
| Provider | Starting Price | Best For |
|---|---|---|
| DigitalOcean | $4/mo | Developers and scalable projects |
| Linode (Akamai) | $5/mo | Technical users, transparent pricing |
| Vultr | $5/mo | OS variety, automation flexibility |
| Kamatera | ~$4/mo | Custom specs and global reach |
| Hostinger | $5.99/mo | Beginners, high RAM on a budget |
| A2 Hosting | $7.99/mo | Speed-focused websites |
| InMotion Hosting | $14.99/mo | Managed VPS for small businesses |
| Namecheap | $6.88/mo | Budget users with basic needs |
| OVHcloud | ~$5/mo | Advanced users in Europe |
| ScalaHosting | $29.95/mo | Business-grade security and support |
Choosing the Right VPS: What Really Matters
Here’s how to simplify your choice:
- Are you a developer? Go with DigitalOcean, Linode, Vultr, or Kamatera
- Need a managed solution? Try InMotion, A2 Hosting, or ScalaHosting
- On a budget? Hostinger and Namecheap deliver great value
- Running a serious business site? Prioritize support and backups with InMotion or ScalaHosting
Click Here For Our Favorite VPS Provider
Final Thoughts
VPS hosting is the next step for anyone serious about growing their website or app. It gives you the freedom to scale, secure your site, and optimize for performance. Whether you’re launching a new project or upgrading from shared hosting, there’s a provider on this list that fits your goals.
Looking to move beyond shared hosting? The right VPS setup can unlock speed, security, and flexibility for your online business. Start exploring your options today and take full control of your website’s performance.
How to Run NordVPN in Docker (Step-by-Step Guide)
Get a NordVPN Account Here
Running NordVPN inside Docker is the cleanest way to protect specific apps, automate privacy, and keep your host system untouched. Instead of installing a VPN directly on your machine, you route only the containers you choose through a secure VPN tunnel.
This guide walks you through the recommended Docker setup used by power users, homelab builders, and anyone running tools like torrent clients, scrapers, or automation services.
Why Run NordVPN in Docker?
Using NordVPN inside Docker gives you several advantages:
- Route only selected containers through the VPN
- Avoid VPN conflicts with your host OS
- Easily start/stop VPN routing per app
- Ideal for servers, NAS devices, and headless systems
- Clean, repeatable, version-controlled setup
The best practice is to run NordVPN as its own container and let other containers share its network.
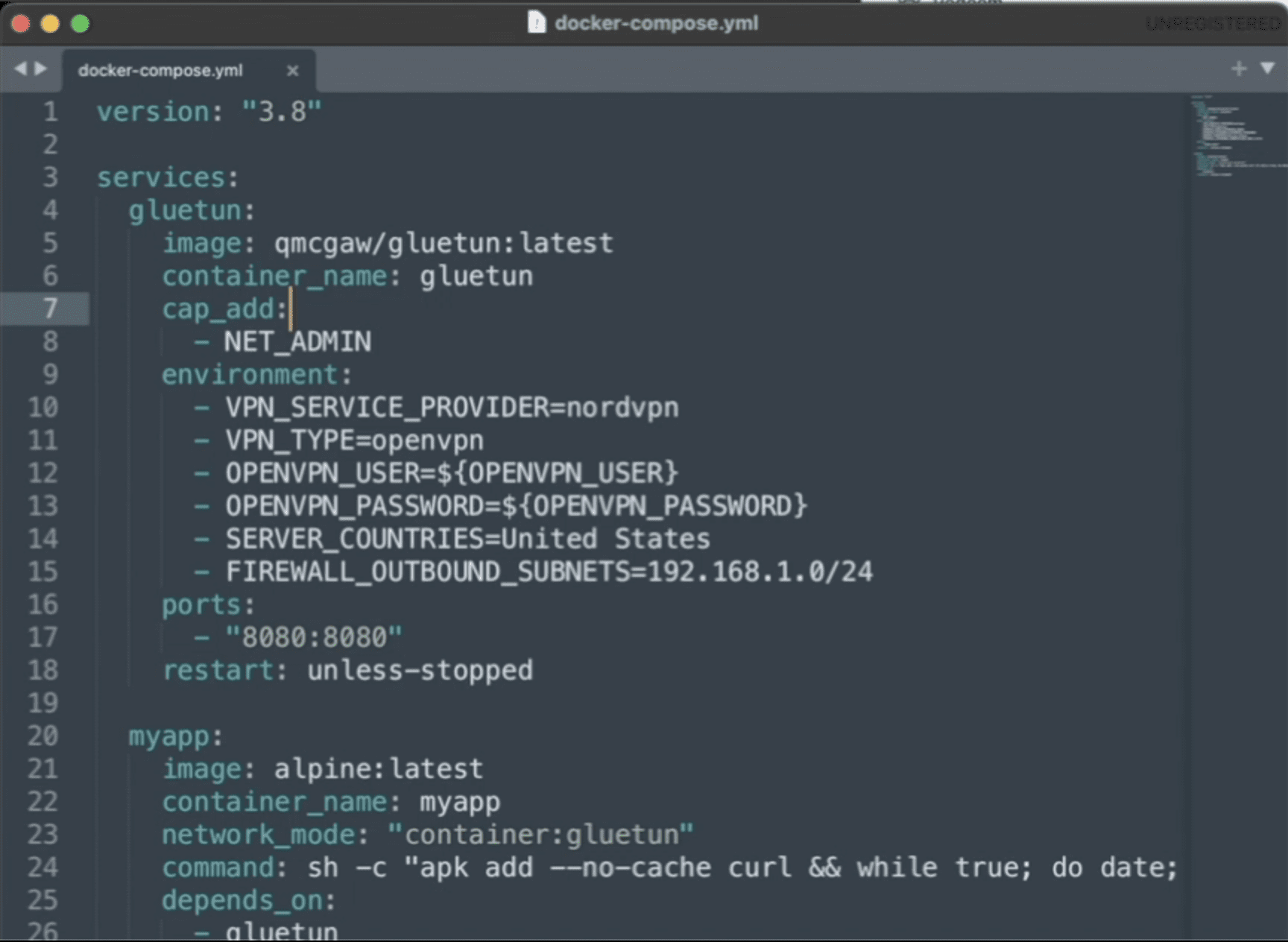
Prerequisites
Before you begin, make sure you have:
- Docker installed
- Docker Compose installed
- An active NordVPN account
- Your NordVPN username and password
This guide assumes a Linux-based Docker host (including NAS devices like Synology).
Get an Active NordVPN Account Here
The Recommended Architecture
Instead of installing NordVPN inside every app container, you will:
- Run NordVPN as a standalone container
- Attach other containers to its network
- Force all their traffic through the VPN tunnel
This creates a single, controllable VPN gateway.
Step 1: Create Your Docker Compose File
Create a new folder and add a file named docker-compose.yml.
What This Does
-
Grants the container permission to create a VPN tunnel
-
Logs into NordVPN automatically
-
Connects to a U.S. server on startup
-
Disables IPv6 to prevent IP leaks
Step 2: Route Another Container Through NordVPN
To force an app to use the VPN, you attach it to the NordVPN container’s network namespace.
Here’s an example using qBittorrent:
Key Line Explained
This forces all traffic from the app container to pass through NordVPN.
Get an Active NordVPN Account Here
Step 3: Expose Ports Correctly (Critical Step)
When containers share a network like this, ports must be exposed on the VPN container, not the app container.
Update the NordVPN service:
Now you can access the app at:
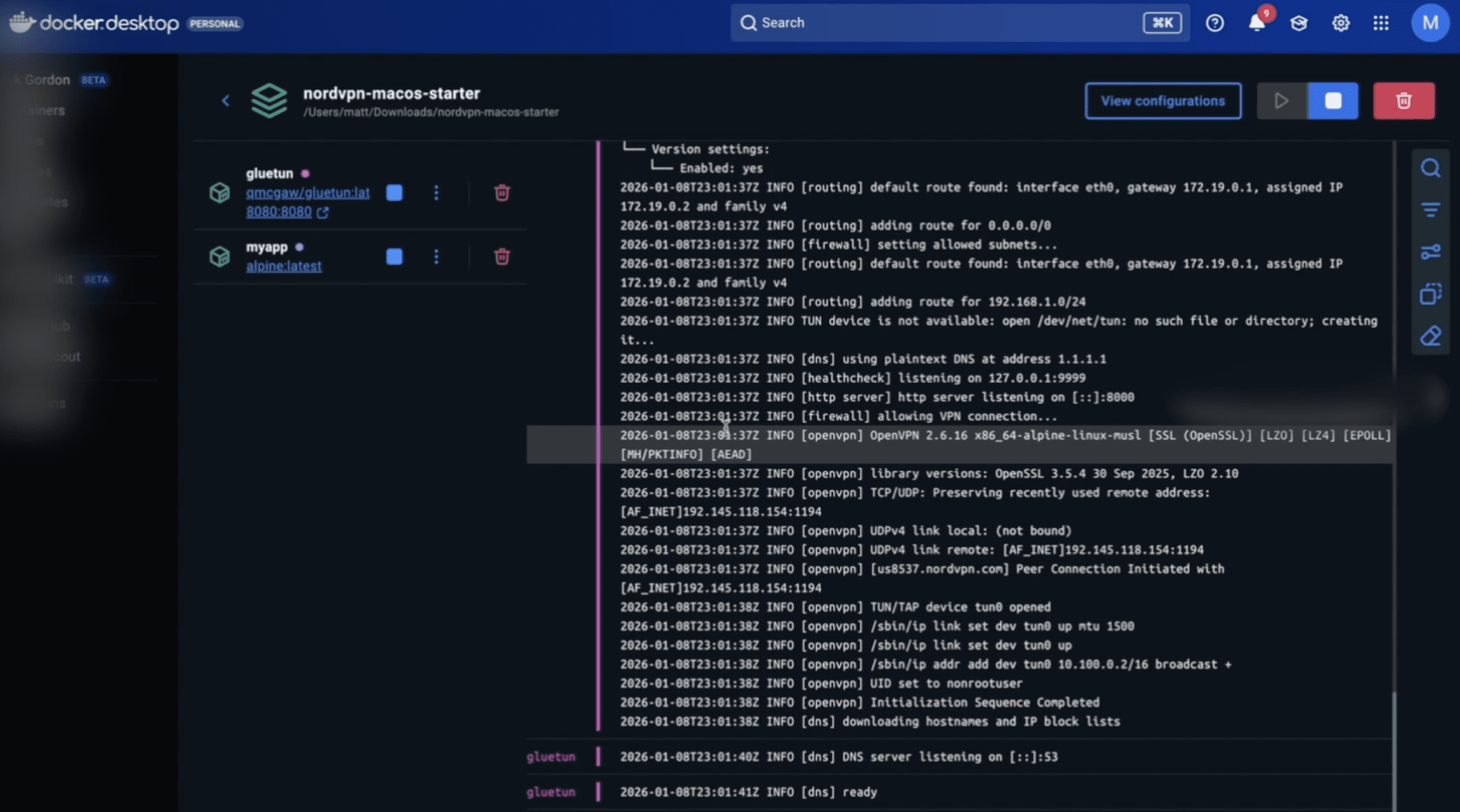
Step 4: Start the Stack
From your project directory, run:
Check the VPN connection:
You should see NordVPN successfully authenticate and connect.
Step 5: Verify the VPN Is Working
Enter the VPN container:
Run:
The IP address returned should be a NordVPN IP, not your home IP.
Any container sharing the VPN network will use this same IP.
Step 6: Add More Containers to the VPN
To route additional services through NordVPN, simply add:
Expose any required ports on the NordVPN container.
Common Mistakes to Avoid
-
Publishing ports on the app container instead of the VPN container
-
Forgetting
NET_ADMINcapability -
Expecting inbound port forwarding (NordVPN does not support it)
-
Mixing VPN and non-VPN traffic in the same container
When to Use a Different VPN Container
If NordVPN authentication changes or you want more flexibility, many users switch to a general-purpose VPN container like Gluetun, which supports NordVPN and many other providers.
The routing concept stays exactly the same.
Final Thoughts
Running NordVPN in Docker is one of the cleanest ways to control privacy, security, and traffic routing in modern containerized setups. Once configured, it’s reliable, portable, and easy to extend.
If you’re running automation tools, scrapers, torrent clients, or server workloads, this setup gives you full control without compromising your host system.
Get an Active NordVPN Account Here
ElevenLabs Pricing Explained (Plans, Credits & API Costs in Plain English)
If you’ve looked at ElevenLabs pricing and thought, “Wait… what’s a credit and how much does the API actually cost?” — you’re not alone.
ElevenLabs uses a credit-based pricing model that’s powerful but poorly explained on the surface. This guide breaks it all down in simple terms so you can confidently answer three questions:
- How much does ElevenLabs really cost?
- How does API pricing work?
- Which plan should I actually choose?
By the end, you’ll know exactly what you’re paying for—and how to avoid overpaying.
Click here to check out ElevenLabs
How ElevenLabs Pricing Works (Big Picture)
ElevenLabs pricing has two layers:
- A monthly subscription plan
- Credits, which act as the internal currency for usage
There is no separate API plan.
Whether you generate audio in the web app or through the API, you spend the same credits from your monthly allowance.
Key idea: If you understand credits, you understand ElevenLabs pricing.
ElevenLabs Pricing Breakdown
What Are Credits (and Why They Matter)
Credits are how ElevenLabs measures usage.
They are consumed when you:
- Convert text → speech
- Generate conversational AI audio
- Transcribe audio (speech-to-text)
In most cases:
- Text-to-Speech consumes credits based on characters
- Conversational AI consumes credits based on minutes of audio
- Higher-quality voices or models may use more credits
Credits reset monthly with your plan. If you run out, you’ll need to buy more or upgrade.
ElevenLabs Subscription Plans (What You Actually Get)
Prices and credit counts can change, but the structure stays consistent.
Free Plan
Best for: Testing and experimentation
- Small monthly credit allowance
- API access included
- No commercial rights
- Limited voices and features
- Good for trying ElevenLabs. Not usable for real projects.
Click here to check out ElevenLabs
Starter Plan
Best for: Hobbyists, light creators, prototypes
- Modest monthly credits
- API access included
- Commercial usage allowed
Works for short voiceovers or small internal tools.
Creator Plan
Best for: YouTubers, podcasters, indie builders
- Significantly more credits
- Better voice options
- API + commercial rights
This is the sweet spot for many users.
Pro Plan
Best for: Heavy creators, SaaS MVPs, agencies
-
Large monthly credit pool
-
Lower effective cost per credit
-
Designed for frequent API usage
Once you’re generating audio at scale, this plan usually makes financial sense.
Scale / Business / Enterprise
Best for: Startups, teams, production systems
- Very high credit volumes
- Priority support, SLAs (Enterprise)
- Negotiated pricing at the top end
If you’re here, you’re optimizing cost per unit—not experimenting.
ElevenLabs API Pricing (The Truth)
Let’s clear up the biggest misconception:
✅ There is no separate API pricing
- API access is included in every plan
- API usage consumes the same credits as the web interface
- No per-request fees
- No hidden API surcharge
You simply authenticate with an API key and spend credits.
Text-to-Speech API Costs (Real-World Explanation)
For standard text-to-speech:
- Credits are consumed based on characters
- Roughly: one credit per character (model-dependent)
Example Scenarios
YouTube voiceover (1,500 words ≈ 9,000 characters):
- ~9,000 credits
Podcast intro + outro (300 words total):
- ~1,800 credits
Blog narration (2,000 words):
- ~12,000–14,000 credits
Higher-quality voices may cost slightly more—but the math stays predictable.
Conversational AI API Pricing
Conversational AI (real-time voice agents, calls, assistants) is billed by the minute, not characters.
Typical pricing:
- Around $0.08–$0.10 per minute, depending on plan and volume
Best use cases:
-
Voice assistants
-
Phone bots
-
WhatsApp or call-based AI agents
-
Interactive voice experiences
This pricing is separate from character-based TTS usage.
Click here to check out ElevenLabs
Speech-to-Text (Transcription) Costs
Speech-to-text consumes credits based on:
-
Audio duration
-
Model used
Common use cases:
-
Podcast transcription
-
Meeting notes
-
Content repurposing workflows
If you’re building a full audio pipeline, factor transcription into your monthly credit needs.
What Happens If You Run Out of Credits?
When you exhaust your monthly credits:
-
Audio generation stops
-
You can:
-
Buy extra credits
-
Upgrade your plan
-
Pro tip:
Upgrading is often cheaper than buying credits repeatedly—especially if your usage is consistent.
Which ElevenLabs Plan Should You Choose?
Choose Starter if:
-
You’re experimenting
-
Usage is light
-
You don’t need much audio each month
Choose Creator if:
-
You’re a YouTuber or podcaster
-
You generate voiceovers regularly
-
You’re building small tools with the API
Choose Pro if:
-
You’re running a SaaS MVP
-
Audio is core to your product
-
Predictable monthly usage matters
Choose Business / Enterprise if:
-
You need volume pricing
-
You need support guarantees
-
Audio is mission-critical
Click here to check out ElevenLabs
Pros & Cons of ElevenLabs Pricing
Pros
-
API included on all plans
-
Simple usage model once understood
-
Excellent voice quality
-
Scales cleanly from hobby to enterprise
Cons
-
Credits feel abstract at first
-
Pricing page lacks real examples
-
Not always cheapest at extreme scale
ElevenLabs vs Other TTS Providers (Quick Take)
ElevenLabs usually wins on:
-
Natural voice quality
-
Emotional tone
-
Ease of integration
Alternatives may win on:
-
Raw volume cost
-
Deep cloud ecosystem integration
If voice quality matters, ElevenLabs is usually worth the premium.
Final Verdict: Is ElevenLabs Worth the Price?
ElevenLabs is priced for quality and developer flexibility, not commodity audio.
If you:
-
Care about how voices actually sound
-
Want API access without complexity
-
Plan to scale usage gradually
Then the pricing model makes sense—and becomes very predictable once you understand credits.
Want to see how to use ElevenLabs audio cleanup feature?
FAQ
Does ElevenLabs charge extra for API usage?
No. API usage uses the same credits as the web app.
Are credits shared between UI and API?
Yes.
Can I use ElevenLabs commercially?
Yes, on paid plans.
What happens if I exceed my monthly credits?
You’ll need to buy more credits or upgrade.
Is ElevenLabs cheaper at higher tiers?
Yes. The effective cost per credit drops as you scale.
Click here to check out ElevenLabs
Docker Commands Cheat Sheet
If you use Docker long enough, you eventually hit the same wall:
-
Containers are running… but nothing works
-
Logs are empty or useless
-
You forget the exact command to “just get inside the thing”
-
Disk space mysteriously vanishes
This Docker cheat sheet isn’t a full reference manual.
It’s the 90% of Docker commands you’ll actually use, written in plain English, so you can move fast when something breaks. This has the most common Docker Compose ports if you need them.
Bookmark it. You’ll be back.
Docker Mental Model (30-Second Primer)
Before commands, anchor these concepts:
-
Image → A blueprint (read-only)
-
Container → A running (or stopped) instance of an image
-
Volume → Persistent data outside container lifecycle
-
Network → How containers talk to each other
-
Dockerfile → Instructions to build an image
-
Docker Compose → Runs multi-container apps
If this mental model clicks, Docker becomes predictable instead of frustrating.
Container Lifecycle Commands
docker run
Create and start a new container.
Most-used flags:
-
-d→ run in background -
-p 8080:80→ map ports -
--name myapp→ name container -
-v host:container→ mount volume -
--env KEY=value→ environment variable
Example:
docker start
Start an existing container.
docker stop
Gracefully stop a container.
docker restart
Quick reset (stop + start).
docker rm
Delete a container (must be stopped).
Force remove:
Inspecting & Debugging Containers
docker ps
List running containers.
Include stopped containers:
docker logs
View container output.
Follow logs:
docker exec
Run a command inside a running container.
If bash doesn’t exist (Alpine images):
This is your “open the sealed box” command.
docker inspect
View detailed container configuration.
Common uses:
-
Find container IP
-
Check mounted volumes
-
Confirm environment variables
-
Debug port bindings
Image Commands
docker images
List local images.
docker pull
Download an image.
docker build
Build an image from a Dockerfile.
docker rmi
Remove an image.
Force:
Volumes & Persistent Data
docker volume ls
List volumes.
docker volume inspect
See where data lives on disk.
docker volume rm
Delete a volume.
⚠️ This deletes data permanently.
Networking Commands
docker network ls
List networks.
docker network inspect
See connected containers.
docker network create
Create a custom network.
Custom networks = cleaner container-to-container communication.
Docker Cleanup Commands
docker system df
Check disk usage.
docker system prune
Remove unused containers, images, and networks.
Aggressive cleanup:
If Docker is eating your disk space, this is usually the fix.
Docker Compose Cheat Sheet
docker compose up
Start all services.
Detached:
docker compose down
Stop and remove everything.
Remove volumes too:
docker compose ps
List running services.
docker compose logs
View service logs.
docker compose exec
Run a command inside a service.
Docker Debugging Shortcuts (Memorize These)
-
Container won’t start? →
docker logs -
Need shell access? →
docker exec -it -
Port not working? →
docker inspect -
Disk full? →
docker system prune -
Data missing? → check volumes
-
Multiple containers? → Docker Compose
Final Thought
Docker isn’t hard.
It’s just unforgiving when you don’t know which command unlocks which door.
This cheat sheet covers the commands that matter—the ones you’ll actually use under pressure.
Stop Guessing: How to Shell Into Your Docker Containers to Debug Errors
You’ve spun up a Docker container. It’s running, but it’s not behaving correctly. Maybe the application is throwing 500 errors, or maybe it’s just silently failing to connect to the database.
You check docker logs, but the output is cryptic—or worse, empty. You feel locked out.
Docker containers are designed to be “sealed boxes.” This isolation is great for stability and security, but it’s a nightmare for debugging when you need to poke around the filesystem to see what’s actually happening.
You don’t need to rebuild the image or add complex logging just to see what’s wrong. You just need to open a side door.
That side door is docker exec.
In this guide, we’ll walk through how to interactively enter a running container, why the command works, and how to handle edge cases like Alpine Linux or permission errors.
Run Docker Free With $200 DigitalOcean Credit
Step 1: Identify Your Target
Before you can enter a container, you need its unique identifier. Open your terminal and list your running containers:
Bash
docker ps
You will see output that looks like this:
Plaintext
CONTAINER ID IMAGE COMMAND STATUS NAMES
a1b2c3d4e5f6 nginx:latest "/docker-entrypoint.…" Up 10 minutes my-web-server
You can target the container using either the CONTAINER ID (the alphanumeric string a1b2c3d4e5f6) or the NAME (my-web-server). The name is usually easier to remember.
Step 2: The Golden Command
To open a shell inside that container, run the following command:
Bash
docker exec -it my-web-server /bin/bash
If successful, your terminal prompt will change. You are no longer on your host machine; you are inside the container, usually logged in as root or the default application user.
From here, you can use standard Linux commands like ls, cat, top, or curl to debug your application from the inside out.
Deconstructing the Command
If you just copy-paste the command, you might not understand why it fails in certain scenarios. Here is exactly what those flags are doing:
-
exec: This tells Docker to run a command inside an existing container (as opposed torun, which starts a new one). -
-i(Interactive): This keeps “Standard Input” (STDIN) open. It allows the container to receive the keystrokes you type. -
-t(TTY): This allocates a pseudo-terminal. It simulates a real terminal environment so you get a command prompt and formatted output. -
/bin/bash: This is the actual command we are running. We are launching the Bash shell program.
Troubleshooting: When /bin/bash Fails
The command above works for 90% of containers (Ubuntu, Debian, CentOS based). However, you will eventually run into an error that looks like this:
OCI runtime exec failed: exec: “/bin/bash”: stat /bin/bash: no such file or directory
This usually happens because you are using a lightweight image, such as Alpine Linux. To keep the image size small, Alpine does not include Bash. It uses the standard Bourne shell (sh) instead.
The Fix: simply change the shell command at the end:
Bash
docker exec -it my-web-server /bin/sh
Advanced Tricks
1. Entering as Root
Sometimes you enter a container, but you are logged in as a restricted user (like www-data or node). If you try to install a debug tool or edit a config file, you’ll get a “Permission Denied” error.
You can force Docker to log you in as the root user (User ID 0) by adding the -u flag:
Bash
docker exec -u 0 -it my-web-server /bin/bash
2. For Docker Compose Users
If you are running your stack via Docker Compose, you don’t need to look up the specific container ID with docker ps. You can use the service name defined in your docker-compose.yml file:
Bash
docker compose exec web_service /bin/bash
A Critical Warning: exec vs. attach
While searching for answers, you might see tutorials recommending docker attach.
Avoid using docker attach for debugging.
-
execcreates a separate process (a side session) alongside your application. -
attachconnects your terminal to the main process running the application (PID 1).
If you are “attached” to the main process and you hit Ctrl+C to exit, you will kill the application and the container will stop. With exec, you can enter and exit freely without affecting the running service.
Want $200 DigitalOcean Credit? Claim It Here
Summary Cheat Sheet
| Goal | Command |
| Standard Shell | docker exec -it <name> /bin/bash |
| Alpine Linux (Lightweight) | docker exec -it <name> /bin/sh |
| Force Root User | docker exec -u 0 -it <name> /bin/bash |
| Using Docker Compose | docker compose exec <service> /bin/bash |
Now that you’re inside, you can check configuration files, verify permissions, or test network connectivity manually. Just remember: containers are ephemeral. Any changes you make to files inside the container will be lost if you delete the container. Use exec for debugging, not for permanent updates.